In prior blog posts and videos we discussed how to use Arrow Builder to create payload-optimized models & APIs and composite models & APIs (data aggregation) from a backend data source without having to write code. In this blog post, we will look at custom fields and how to add and set them from the admin console (i.e. in the browser with no coding required).
Let’s get started by describing what Custom Fields are.
Custom Fields are fields that don’t exist in the backend data source. For example, say your backend system returns FirstName and LastName but in your app you would like to display FullName. Of course, you can combine the two in the app logic, but part of the value of a middleware solution like Arrow is to provide optimized APIs so the data is returned precisely as the app needs it. This eliminates the need for the developer to do this work in the app, which makes the app more lightweight, responsive and easier to maintain.
You can read more about Custom Fields and Arrow Builder in the online docs here.
Now let’s describe one way to add custom fields to a model.
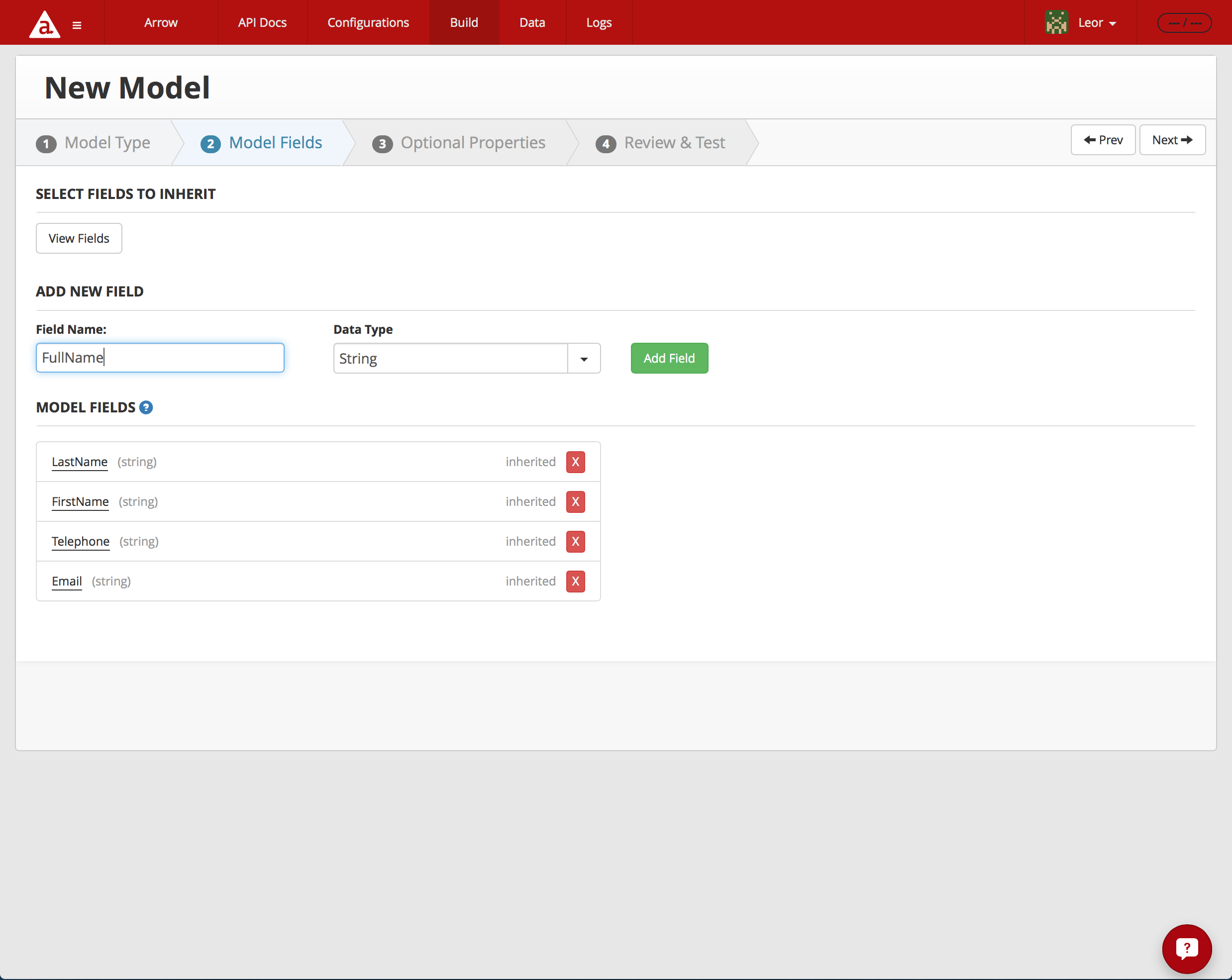
In the screen shot below, I am using the Arrow Admin Console to create a model, called MyContact, which is a reduced Salesforce Contact model. I selected to inherit LastName, FirstName, Telephone and Email fields. Those are listed in the Model Fields section of the page. In the Add New Fields section, I create two new custom fields by entering the Field Name and selecting the Data Type from the picker and pressing the Add Field button.
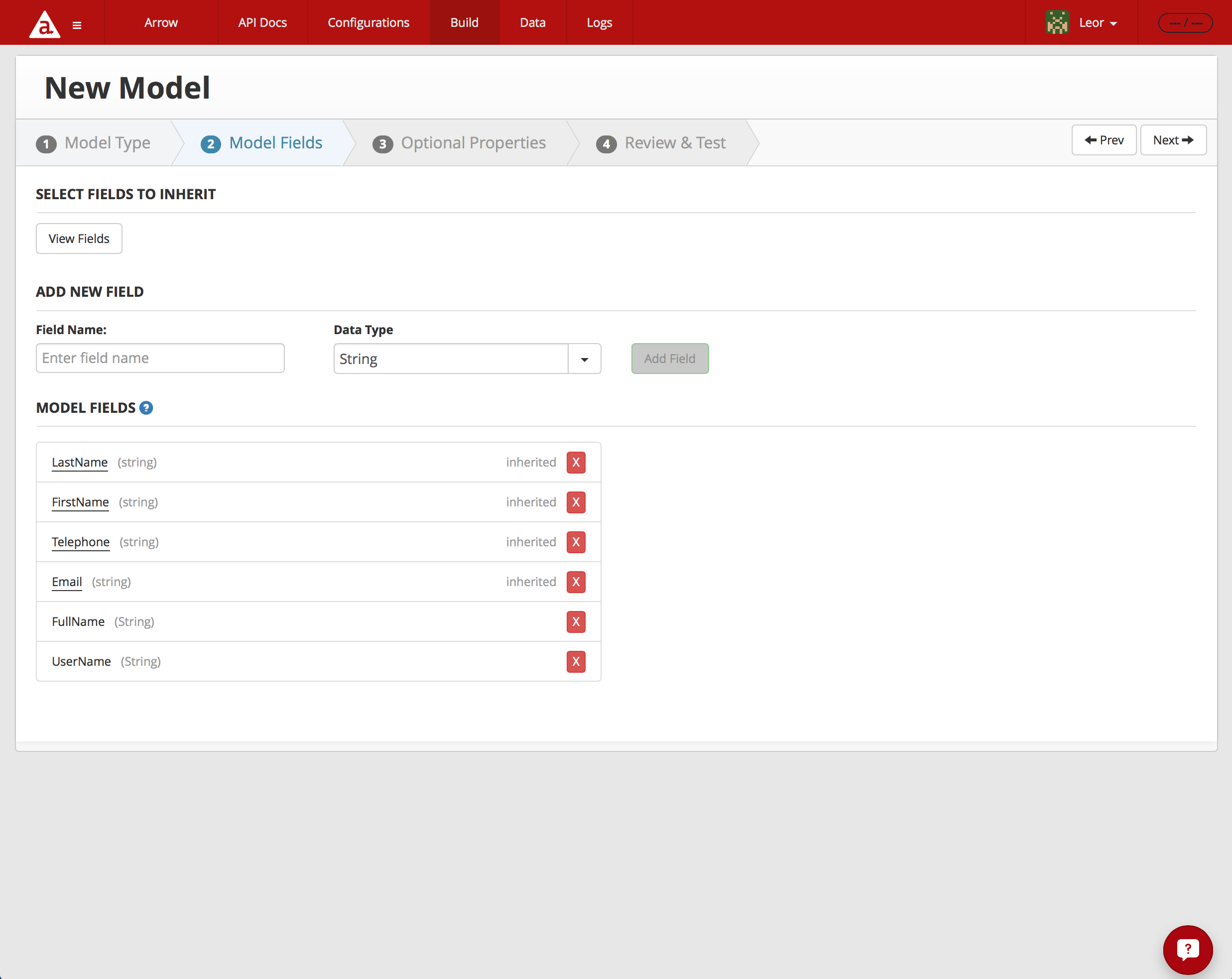
When I’m done adding my two custom fields, FullName and UserName, you can see them added to the Model Fields a section of the Model Fields screen below.
How do we populate the data for these custom fields?
In my example, I want to return FullName as the string concatenation of FirstName and LastName. We will use the get property of the Field in order populate it as follows:
return model.FirstName + ' ' + model.LastName;
Click on the FullName line in the Model Fields as shown below.
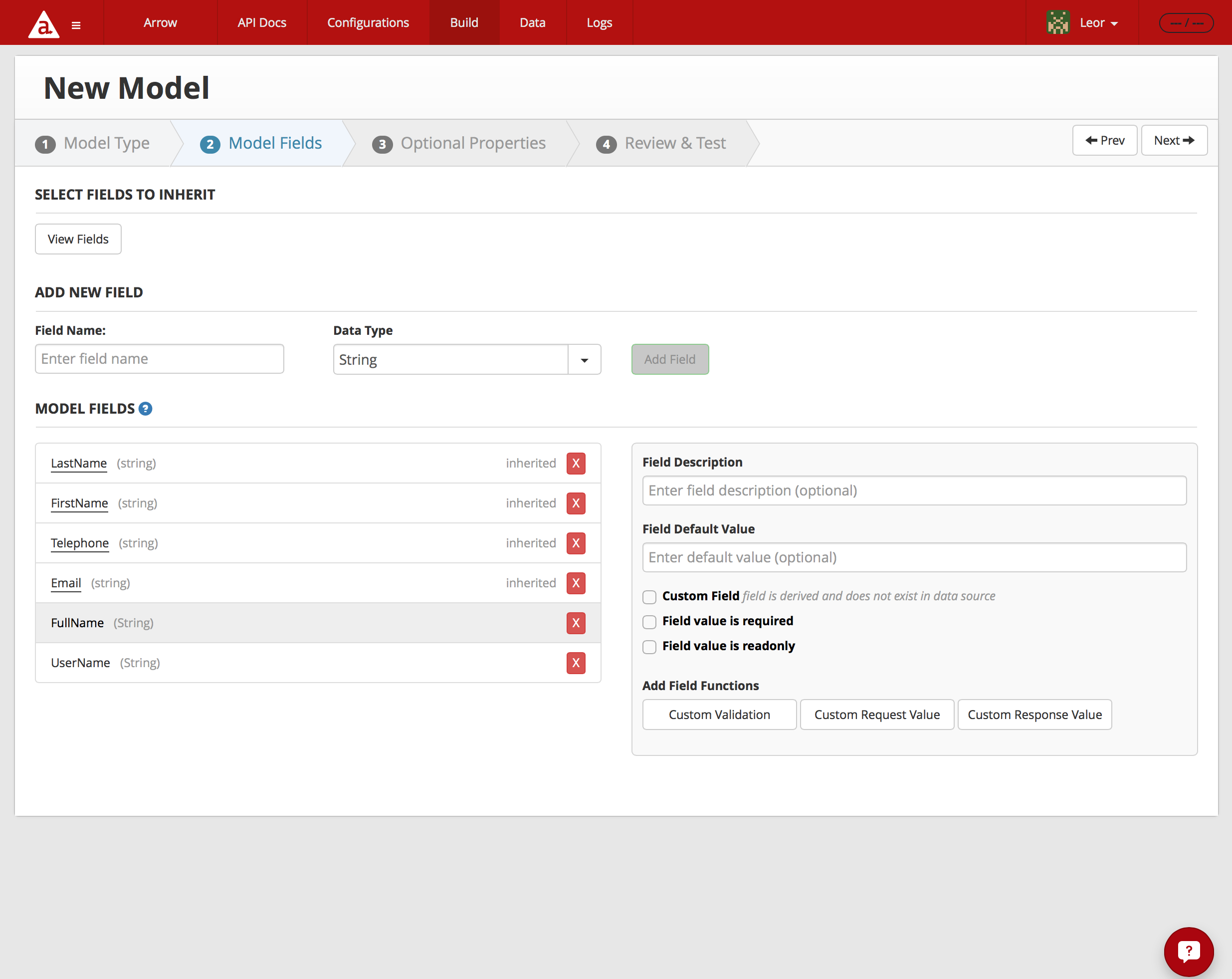
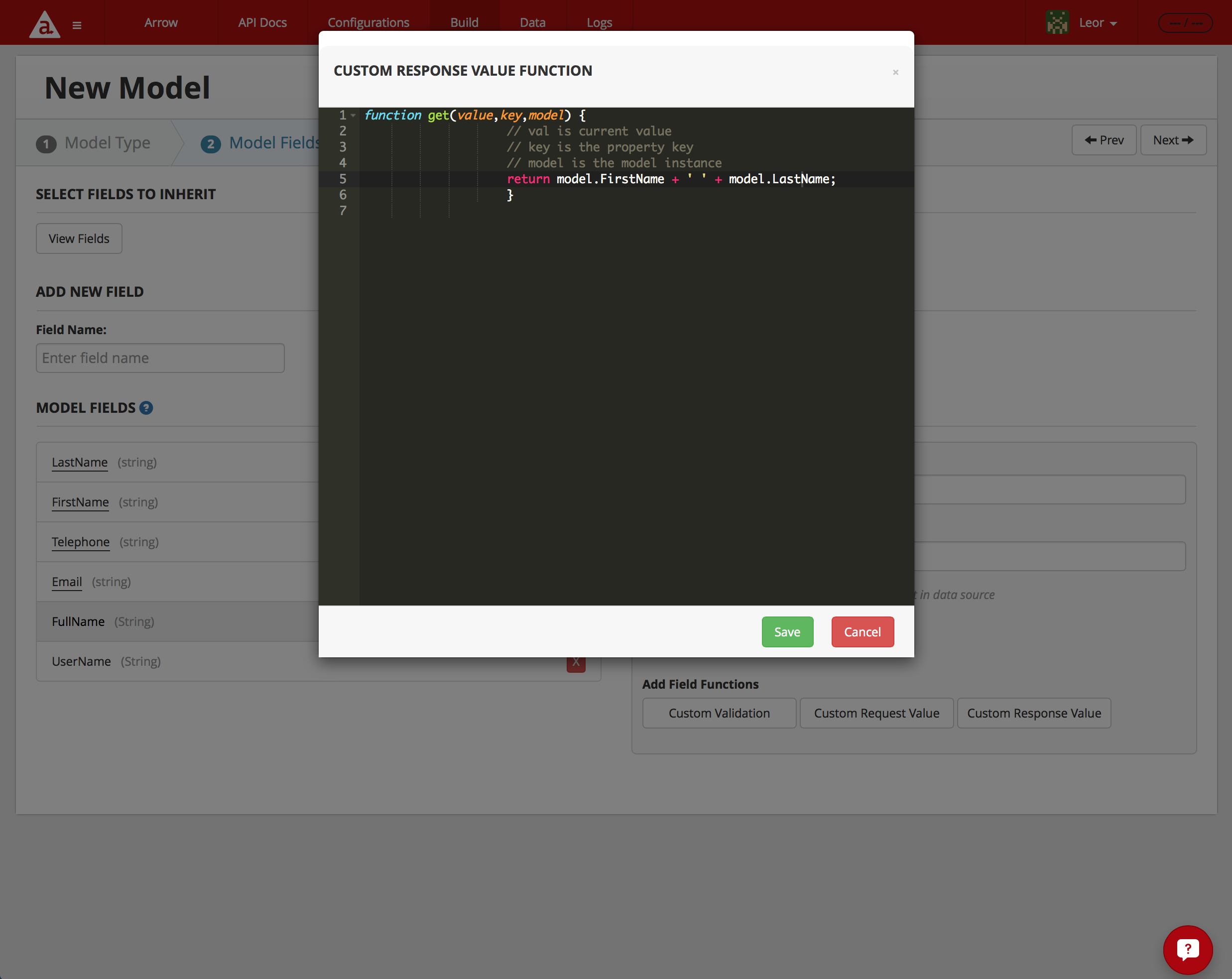
Then click on the Custom Response Value button as show below. This will bring up a dialog box where you can define the function to set the field.
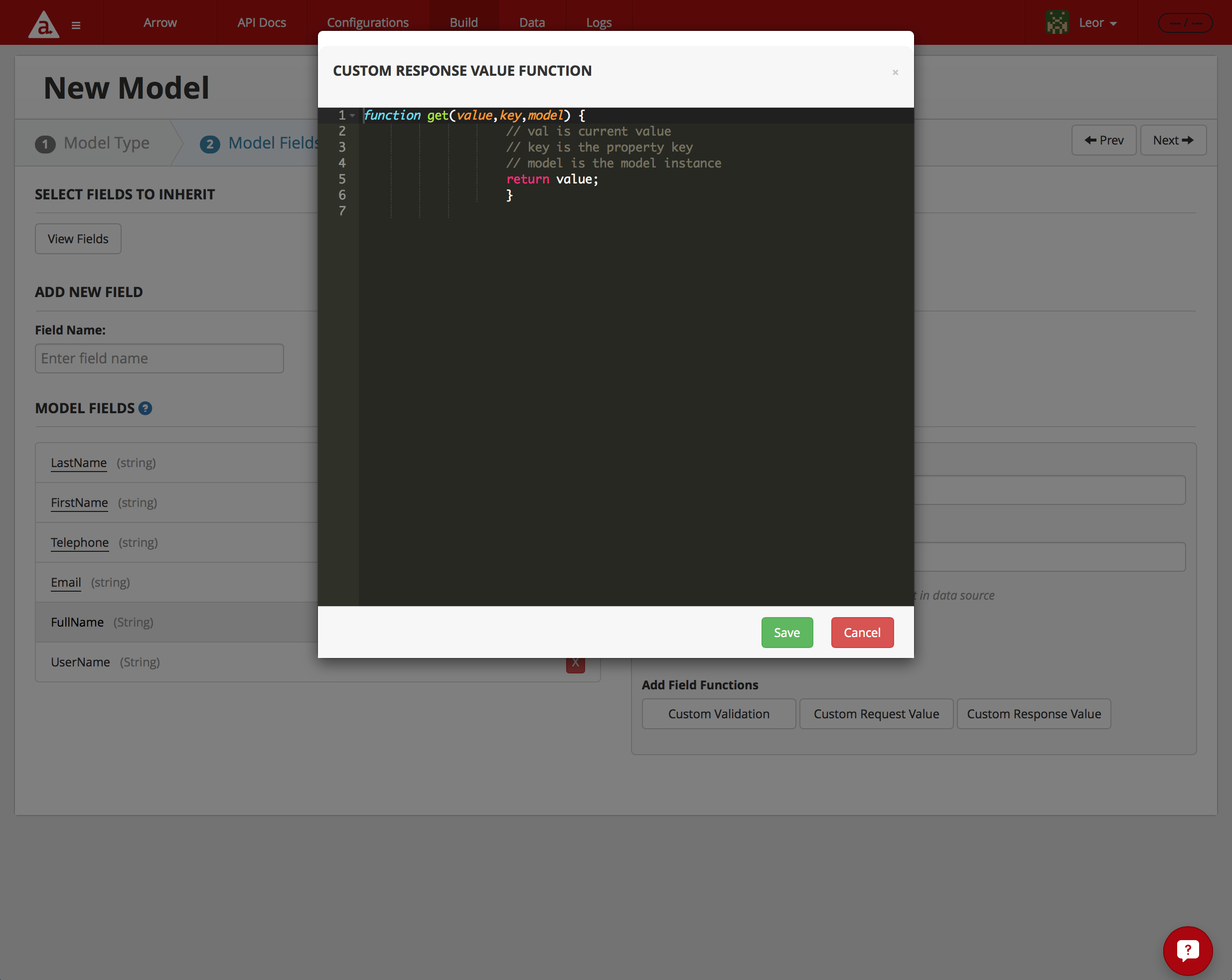
Enter the JavaScript for setting the Custom Field based on other fields in the model as shown below.
In my example, I also want to return the contact’s UserName which is extracted from the contact’s email address as follows:
return model.Email? model.Email.split("@")[0] : model.Email;
The code above strips away the @ and everything afterwards, leaving just the contact’s username.
I am using the JavaScript ternary operator to first check if Model.Email exists before using the JavaScript string split() operation and then I’m returning the first element of the array. Learn more about string split() here.
After completing these operations I end up with the following MyContact model:
var Arrow = require('arrow');
var Model = Arrow.Model.reduce('appc.salesforce/Contact', 'mycontact', {
fields: {
LastName: {
type: String,
description: 'Last Name',
maxlength: 80,
required: true,
optional: false
},
FirstName: {
type: String,
description: 'First Name',
maxlength: 40
},
Telephone: {
name: 'Phone',
type: String,
description: 'Business Phone',
maxlength: 40
},
Email: {
type: String,
description: 'Email',
maxlength: 80
},
FullName: {
type: String,
get: get_FullName
},
UserName: {
type: String,
get: get_UserName
}
},
actions: [
'create',
'read',
'update',
'delete',
'deleteAll'
]
});
function get_FullName(value,key,model) {
// val is current value
// key is the property key
// model is the model instance
return model.FirstName + ' ' + model.LastName;
}
function get_UserName(value,key,model) {
// val is current value
// key is the property key
// model is the model instance
return model.Email? model.Email.split("@")[0] : model.Email;
}
module.exports = Model;
See how Arrow Builder cleans up the code and creates methods for get_FullName and get_UserName.
If I call this model’s FindAll method, I get the following data:
{
"success": true,
"request-id": "b9448871-74de-40c1-8b38-bfc81bd153c6",
"key": "mycontacts",
"mycontacts": [
{
"id": "003i000000M33B3AAJ",
"LastName": "Gonzalez",
"FirstName": "Rose",
"Telephone": "(512) 757-6000",
"Email": "rose@edge.com",
"FullName": "Rose Gonzalez",
"UserName": "rose"
},
{
"id": "003i000000M33B4AAJ",
"LastName": "Forbes",
"FirstName": "Sean",
"Telephone": "(512) 757-6000",
"Email": "sean@edge.com",
"FullName": "Sean Forbes",
"UserName": "sean"
},
.
.
.
{
"id": "003i000000M33BMAAZ",
"LastName": "Llorrac",
"FirstName": "Jake",
"FullName": "Jake Llorrac"
}
]
}
So, once again we see how powerful the Arrow Admin Console is for helping to build out more complex API features with no code or low code.
Follow us on social