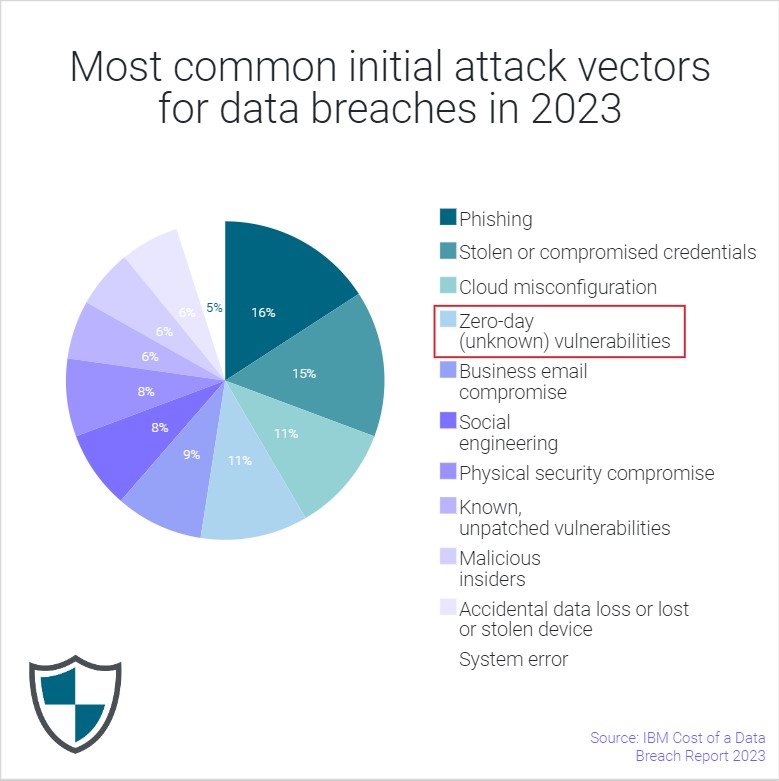
It’s not an overstatement that secure data and file transfers are a top priority virtually everywhere today. 2023 saw the discovery of 15 critical vulnerabilities, with some 62 million people’s personal data compromised.
From stolen or compromised credentials to malicious insider attacks, zero-day vulnerabilities, or cloud misconfigurations, MFT teams across regions and in all industries are facing a once-in-a-generation file data breach crisis.
With billions of dollars at stake to keep valuable and sensitive data secure, it’s more important than ever to trust your managed file transfer solution. Many vendors are learning the hard way that security is a shared responsibility, and it is critical to put in place the right framework to protect and be proactive.
Here’s a look at why so many enterprises are consolidating MFT operations and switching to more secure, cloud-based product and service vendors.
Growing adoption of cloud MFT
Enterprises need to be able to innovate and grow their business without inopportune interruptions and incidents. Modern managed file transfer (MFT) provides a reliable way to transfer critical business data internally and externally, with built-in security features like data encryption.
Meanwhile, new controls and architectures are helping accelerate MFT services delivery. Eliminating any downtime of MFT operations with Sys/Dev-Ops automation has become a priority requirement.
In a world of digital transformation, cloud-based managed file transfer solutions simply make sense from a scalability, flexibility, and cost standpoint.
Cloud MFT solutions are owned and operated by third-party providers, requiring less maintenance and upgrades from internal IT teams. Cloud MFT is faster and more cost-effective to set up and can be configured in flexible cloud deployments.
Yet there is a common hang-up in the adoption of cloud MFT solutions, as with other cloud solutions: questions around security.
How secure is cloud MFT?
Many people tend to see information as safer stored on premises than it is in data centers managed by large cloud providers.
But the reality is that data stored on a laptop – which can be easily stolen – is more at risk for a breach than data hosted on major cloud providers such as Amazon Web Services (AWS) or Microsoft Azure.
That’s because these providers are backed by the work of world-class security experts to create an infrastructure that meets today’s most stringent security standards. And with a managed cloud service, the managed cloud MFT provider has a team of experts actively involved in protecting your enterprise against the latest threats.
File transfer software has undergone significant evolutions
There is growing demand for MFT in the cloud that is always up and fully secured. New controls and architectures help accelerate MFT services delivery (i.e., cloud, outsourcing, hybrid, DevOps, full service), while the disruption of long-standing security positions usher in the beginning of a Zero Trust approach for MFT.
Modern managed file transfer solutions include end-to-end encryption, audit trails, and access controls that make it harder for cybercriminals to access sensitive information.
Built-in alerts also provide an additional layer of security. Your IT team can configure the real-time alerts on file transfer completion based on a set of rules that your company creates.
Possible alerts could include:
- Sending
- Sent
- Receiving
- Received
- Failed
- Canceled
- Temporary Failed
- Permanently Failed
Every event, whether it’s the commencement of a transfer, its completion, or failures, should be logged to a central database by your MFT solution. It’s just another feature that adds to the security of cloud MFT solutions.
Monitoring file transfer activity from a single administration console offers end-to-end visibility that makes it easier to detect recurring patterns in file transfers (for better or for worse) and prevents blind spots that can ultimately lead to cybersecurity breakdowns.
Predictive analytics help IT personnel properly assess vulnerabilities at a glance. And automated workflows allow teams to encrypt and transfer files according to their organization’s requirements.
Modern MFT solutions leverage APIs to help configure and provision file transfers or integrate applications. Traditional MFT integrations involve quite a bit of coding, as well as an expert understanding of IT processes. Intelligent MFT, on the other hand, simplifies things by offering a visual programming tool that uses a set of connectors to make MFT integrations more intuitive.
Embracing Sys/Dev-Ops automation has practically become a requirement, as it allows enterprises to bolster their security posture, streamline operations, and ensure compliance with evolving regulatory requirements.
See also: Why MFT matters for enterprise compliance
We even speak of “self-healing” MFT today, especially as it becomes more and more difficult to maintain MFT-skilled staff. The features described above around monitoring, analytics, and API-driven commands contribute to automation so that a system can autonomously detect and resolve issues or errors that arise during file transfer processes.
This enables the MFT system to maintain continuous operation and ensure the reliable and secure transfer of files without the need for manual intervention – even in the face of unexpected disruptions or failures.
A proven track record is the greatest MFT security benchmark
One final but critical element in evaluating the security of cloud MFT solutions is a provider’s track record.
Enterprises can’t afford to gamble with security of their critical infrastructure – and that’s precisely what MFT is for many organizations today. A data breach cost on average $9.48M in the U.S. last year – and it’s even higher ($10.9 M) for healthcare companies.
And when one out of ten enterprises reported they recently experienced a breach because of a vulnerability they didn’t even know to look for, it’s always a good time to reevaluate the strength of your MFT security.
One of the surest markers of trust for an MFT product is if the provider has a long track record of security and resiliency in large enterprise cloud file transfer.
Elevating data security amidst increasing active threats is Axway’s strength. We offer best in class scale, pattern coverage, and experience.
Axway started managed cloud operations for MFT more than ten years ago, serving government agencies like the IRS. This means it was essential for our personnel to have high security government certifications, and that same DNA fueled our expansion to more government, financial services, and healthcare organizations that have the highest levels of security provisions.
Today, Axway manages hundreds of thousands of connections and partner access points securely, processing millions of files per day – without any major breach or security issue. Our robust encryption practices set us apart from more basic MFT solutions.
This level of secure service capability should be the benchmark for any MFT solution.
Furthermore, a trusted vendor should be committed to staying up to date with the latest security threats and will take proactive steps to mitigate these threats. They will be transparent about their security practices and will work with customers to ensure that the solution is as secure as possible.
Axway continues investing to update, modernize, and innovate in this domain. We also have a strong Secure Software Development lifecycle in place that defines a security gate to be reached by each Axway product before being released to customers, including attack surface analysis, dynamic application security testing (DAST), static application security testing (SAST), container security analysis, and manual penetration testing.
See also: Ensuring your data stays protected from cybercriminals targeting MFT vendors
One way to get a sense of an MFT provider’s track record is by consulting user reviews. G2, the world’s leading business solution review platform, collects peer user reviews and also rates software products to determine quarterly awards and leadership.
Discover Axway Managed File Transfer Reviews & Product Details on G2.
Best practices for secure cloud MFT
Beyond choosing a reputable provider with a strong track record of security, some best practices for cloud MFT security include:
- Implementing access controls and encryption
- Conducting regular security audits and assessments
- Training employees on cloud MFT security best practices
- Adopting a Zero Trust approach to enterprise security
- Keeping MFT software up to date at all times.
We’ve covered the Zero Trust security model for MFT in greater detail over here, but the following first steps give you a sense of how a Zero Trust security model is crafted:
- Catalog and understand the data being moved through your system
- Determine how and where you’re going to centralize your identity
- Determine the governance model for each of the individual data flows
- Enable infrastructure visibility and connect it to AI and SIEM technology
- Rationalize your current and future plans in terms of your MFT systems
Download the checklist: 5 steps you can take to move toward Zero Trust security
No single solution can deliver Zero Trust security – rather, MFT and cloud providers can work alongside customers and providers to validate appropriate solutions and provide guidance along the Zero Trust security journey.
Meetesh Patel, General Manager of Managed File Transfer at Axway, describes in the following video clip from a webinar how a growing MFT footprint naturally leads to greater risk if enterprises aren’t vigilant.
Another essential practice for securing files and data is keeping MFT systems up to date. Teams often drag their feet on these because they’re hesitant to disrupt business, yet failing to perform updates opens their organization up to vulnerabilities.
It’s why zero downtime updates are becoming a reality, appealing especially to those with high-value file transfer operations relying on uninterrupted service, necessitating 24/7/365 availability.
Axway MFT is leading the charge to secure MFT
Axway can offer peace of mind to our customers. We protect your files and take care of all technical complexity so that our customer can concentrate on their business growth.
With the choice to be hosted on AWS or Microsoft Azure, Axway’s cloud MFT solutions provide businesses with the experience they want without the weight of security or cloud sovereignty concerns. Businesses can deploy into the cloud at their own pace and desired configuration.
Building on the security capabilities included in major cloud providers’ infrastructure, Axway delivers a centralized command and control layer that makes it easy to visualize file transfer activity in a non-technical manner. Without having to write any sophisticated code, business users can manage file transfer setup in a self-service way and access proactive insights before an impact is felt.
Axway protects your enterprise against the latest cloud-based security threats, vulnerabilities, and intrusions with the most robust security accreditations available.
Consider how Axway helped Textron, a multi-industry company with a global network of aerospace, defense and intelligence, industrial, and financial businesses, secure its MFT landscape.
“As soon as we moved to Axway Managed Cloud Services for MFT, we finally got our weekends back!” says Al Gutierrez, IT Senior Architect at Textron. “We no longer need to spend our days and nights remediating vulnerabilities and firefighting technical issues — with the Axway Cloud, we can focus on delivering value-added services to the business.”
Hear more about Textron’s story below:
From day one, Axway’s suite of MFT solutions act as if they have been part of your company’s IT infrastructure, supporting a complete ecosystem that is built for reliability, security, and cost-effectiveness.
We are creating a framework to facilitate automation, time to production, and revenue recognition, while at the same time providing total transparency against entitlement and usage, ensuring security and compliance, and ultimately providing the best user experience by abstracting away ecosystem complexity.
Plus, it’s hard to beat platinum-level SLAs with 99.99% availability.
Let us help you simplify your approach to managed file transfer, and we’ll develop a secure MFT solution that is right for your organization.

Follow us on social