I recently watched the courtroom scene from A Few Good Men where Jack Nicholson’s character, Colonel Jessep, takes the stand to determine if a code red, aka hazing ritual, was ordered or not. As the rookie attorney, played by Tom Cruise, starts to crank up the heat, the Colonel cracks and utters the now-famous line: “You can’t handle the truth.”
In the monologue, the Colonel rants about the need to have someone guarding the walls and that the responsibility is far greater than the rookie attorney can know. This immediately reminded me of the API Gateway! No, really, I am serious–just consider the breadth and depth of functionality that an API Gateway provides: guarding an organization from cyber threats, routing traffic, load balancing, and on and on… Most enterprises are unaware of the full breadth and depth of an API Gateway. In this blog, I will summarize API Gateway capabilities as it stands on the wall.
READ MORE: Why you need an API Gateway and security.
API Gateway capabilities — at the edge of the enterprise
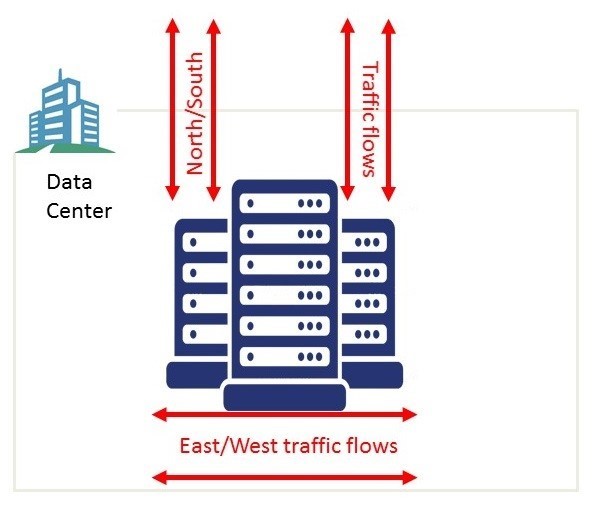
API Gateway are battle-hardened for managing API traffic. The Gateway is deployed as a proxy for management of North-South traffic and is traditionally deployed in the Demilitarized Zone (DMZ) of the enterprise. North-South traffic describes the client-to-server traffic that moves into the data center from a location outside of the data center. The term North-South comes from network diagram drawings that usually depicts wide area network (WAN) traffic vertically. For API Management, North-South traffic is the external traffic which comes from external clients (API consumers) across the DMZ and arrives at some endpoint behind the DMZ.
Border control–authentication, authorization, audit

The Gateway provides the enforcement capability that only trusted messages (authentication and authorization) can pass through– just like when you enter a country, the border control requires that you produce the appropriate documentation. For example, a passport to verify your identity and a perhaps a visa to prove that you are allowed to cross the border. The Gateway provides multiple ways for API consumers to authenticate and get access to API resources. The Gateway can support one of the many open standard that means to determine the validity of an API Consumer (i.e., OAuth, JWT tokens, API Key, HTTP Basic/Digest, SAML, etc.) or it can use non-standard means to locate credentials in headers or payload of the message.
In addition to authentication and authorization functions, the Gateway can inject additional metadata information into the message about the original API Consumer (IP address, roles, attributes, claims, etc.). Thus, identity information of the API Consumer flows into an organization so that downstream consumers have context about the original sender. The identity propagation may be in the format of a new JWT claim or SAML token or simply inserted into the payload. This is similar to how border control will stamp a passport with the date and entry details in a passport of a person crossing the border.
The Gateway may call out to another system in order to determine if the message is allowed to pass through. For example, it could call out to an external Identity Provider or authorization system. Similarly, a customs agent might check an individual’s information against a known database for criminals.
Every call passing through the Gateway is logged and contributes to the audit trail of who, why, what and when an API Consumer invoked an API.
Customs examination–threat protection

The Gateway prevents attacks by inspecting the messages passing through it. The Gateway provides API firewalling, content validation and message integrity checks which are in place to only allow legitimate messages to enter an organization.
- API Firewalling helps to mitigate against application-level threats, such as cross-site scripting, SQL injection, command injection, cross-site request forgery, etc. The Gateway will detect and block threats (i.e. OWASP top 10). Additionally, messages can be checked to see if they might contain viruses.
- Content validation is the ability to ensure that the request is appropriate for the requested API. The validation will check that the incoming request (and response) contains the appropriate parameters and values and that the payload adheres to the APIs schema.
- The Gateway will verify the integrity of the signed message (signed tokens, headers, payloads) to confirm that the message has not been tampered with in flight. In addition, it can ensure that some aspects of the payload remain confidential by encrypting, etc.
The Gateway can act as an enforcement point which can delegate to a third-party system to make a decision on whether the message is good or bad (i.e., call ICAP server, PingIntelligence, etc.). The Gateway will enforce the decision from the third-party system.
Transformation
The Gateway provides a transformation layer which can transform all aspects of the incoming request, from the protocol, payloads and headers to the security tokens.
- Protocol mapping: The Gateway can translate between protocols which the API Consumers support (i.e., HTTP or WebSockets) and translate this to protocols which are supported internally in the enterprise (i.e., JMS, AMQP, MQTT, gRPC, etc.).
- Transformation: The Gateway can transform the contents of the payload into a format which is accepted internally (i.e., JSON to XML/SOAP) or it can modify headers.
- Security tokens and claims can be inserted into messages as they flow internally so that information determined at the edge is made available internally.
Traffic Management

As the Gateway sits in the line of traffic, it provides basic load balancing capabilities (Round Robin, Weighted Round Robin, random, etc.) for traffic entering the organization.
The Gateway provides various mechanisms for managing the rate of flow into an organization. It can protect your backend against severe traffic spikes and denial of service attacks.
As it sits in the flow of traffic it can provide traffic throttling and smoothing. IP addresses can be white or blacklisted. Additionally, the Gateway provides various failure patterns, like a circuit breaker or retry policies, to help protect the organization from cascading failures.
READ MORE: Learn about API Gateway to the Cloud.
Monitoring and visibility
Finally, since the Gateway controls all inbound traffic, everything can be logged, which allows for visibility, reporting and analytics services to be applied. The Gateway is able to highlight to an organization the status of the APIs that are known and governed and also highlight traffic which is currently ungoverned.

The API Gateway capabilities can provide usage reports to API Consumers and to the API Provider so that they can see the traffic and trends related to their API and applications. It can provide detailed traffic logs for the API provider to help with debugging of internal infrastructural issues.
“You can’t handle the truth!”
Coming back to the speech from Jack Nicholson’s A Few Good Men: “We live in a world that has walls, and those walls have to be guarded…I have a greater responsibility than you could possibly fathom”. In the API world, while not Guantanamo Bay, there is still the requirement that its many boundaries within your enterprise be guarded and that role is multifaceted. Your best bet under these circumstances is to employ the help of the API Gateway as your “Marine” on the wall.
Learn about the role of the API Gateway in the modern enterprise.

Follow us on social